You're Writing Animals Wrong
A humorous take on animals as poorly designed software platforms, cataloging their biological quirks as bugs, architectural flaws, and undocumented features through the lens of software development.
Animals are platforms with very limited memory, computational capabilities, and modification potential. The developers working in the animal domain produce remarkably ingenious low-level algorithms. However, extensive hardcoding creates characteristic problems due to the lack of proper testing under exotic conditions. Input filtering is implemented poorly.
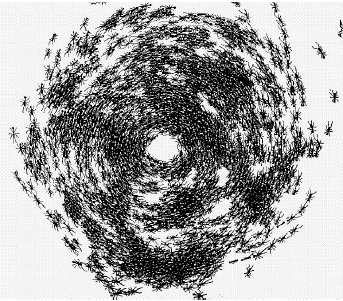
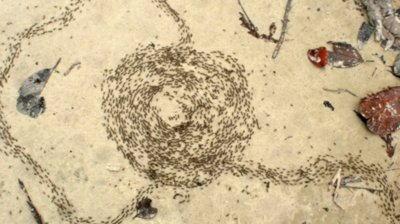
Navigation Algorithm Vulnerabilities
The ant navigation system demonstrates recursive algorithm flaws, creating what is known as a "death spiral."
Bird Implementation Issues
Most birds contain a critical vulnerability allowing "arbitrary egg injection into nests." Birds verify only egg placement and quantity, but not their cryptographic hashes. Cuckoos exploit this 20% of the time while maintaining checksum validity — sufficient for privilege escalation within the nest.
The "friend-or-foe" recognition module contains severe flaws. This enables animal-in-the-middle attacks using chick vocalization substitution. Anything matching the expected size and transmitting the exposed key portion requires feeding. Similar bugs appear in rodents, suggesting shared library functions.
Lizard Architecture
Lizards execute running functions in one process while breathing in another. The platform lacks multitasking support, so the workaround limiting maximum run duration to 4-6 seconds deserves special mention.
Ant Behavior Loops
Ants easily enter infinite loops. Their navigation combines with OS priority systems, creating "spirals of death" that drain increasingly more colony resources over 3-4 days until starvation or an external navigation change breaks the cycle.
Ostrich Optimization
The ostrich's digestive implementation represents engineering excellence. It naturally consumes stones, and during running these grind grain for processing. The developer disabled central vision sectors (similar to rabbits) to avoid writing separate stone-eating code. Consequently, ostriches hit grain targets only 30-50% of the time, enabling adequate stone accumulation.
Ostriches in clean virtual zoo environments experienced digestive problems before hypervisor-level stone support was added. Cattle also consume nails and gravel, but this reflects backward compatibility issues rather than core architecture.
Crocodile Reuse
The stone-swallowing functionality was ported to crocodiles for better diving capability. It worked well.
Energy Consumption Solutions
Reptile platforms handle this acceptably since extended high-level processes don't exist. Crocodiles remain motionless for days awaiting prey capture. Large carnivores operate differently.
Lions disable active processes for approximately 20 hours daily, entering sleep mode. They remain active for roughly 4 hours — vocalizing, reproducing, exploring savannas, and locating recharging opportunities through antelope or zebra encounters.
Dolphins cannot consistently activate both brain cores, only during important tasks. Encountering a sluggish dolphin? Check whether both eyes are open. Only one? It's running in sleep mode at reduced clock frequency.
Bears don't always exit hibernation correctly. Some plants share this bug, but it's less dangerous since plants restart easily. The albatross developer deserves special recognition — it sleeps while flying.
Turtle Implementation
Rather than programming proper obstacle avoidance, developers hardcoded head-retraction reflexes. When encountering crocodiles with their lightning-fast strikes, this prevents decapitation. Interestingly, turtles easily evade butcher knives. Hardware-level instruction processing exceeds interpreted higher-level code performance. Turtles won't be outrun — critical functions utilize assembly language.
Polar Bear Solar Engineering
Polar bears exemplify solar energy implementation brilliance. They are transparent to ultraviolet in their fur but have black skin underneath — a genuine engineering triumph.
Giraffe Implementation
Giraffes represent pure workarounds. Client requirements for canopy height increased repeatedly during development. However, water access requirements from release acceptance testing were ignored — a catastrophic oversight. Giraffes cannot reach water normally. They require awkward contortions, nearly doing the splits just to drink. Naturally, predators exploit this ruthlessly. Calves require reinforcement as well — they literally fall from 1.5 meters at birth during the stable release.
Guinea Pigs and Fish Issues
Guinea pigs and certain fish have incorrectly implemented interrupt delays. Normal animals poll interrupts sequentially — danger checks, hydration needs, feeding requirements, reproduction prompts, sleep needs, and non-standard procedure execution — without apparent switching. Guinea pigs execute sleep(1000) post-operation. This is likely debug code that made it into production.
Squirrel Garbage Collection
Porting goldfish garbage collection code to squirrels worked out well. The collector clears unused pointers to marked nut and seed locations with high probability. Consequently, many new trees grow thanks to squirrels.
Indian Cobra Design
The Indian cobra was certainly written by StarCraft fans. Where else do you encounter units that spit venom 2.5 meters directly into an opponent's eye?
Octopus Complexity
The octopus represents irrational design — kilometers of nervous tissue simply because someone enjoyed brainfuck programming. Those separate suction-cup control modules might constitute a data center on wheels if properly utilized.
Penguin Implementation
Penguins cannot fly but swim excellently and jump up to half a meter in height. They were developed as educational polymorphism examples, but library dependencies somehow remained in the stable release.
Insect Recursion
Aphids and insects were written by recursion enthusiasts. The concept of bearing already-pregnant offspring creates testing nightmares. Meanwhile, elephant calves take 22 months to deploy — failing to fit in the processor cache.
Hippopotamus Easter Egg
The hippopotamus easter egg is quite entertaining. Humans fear lions, rhinoceroses, and snakes — yet this charming heavyweight deliberately pursues humans at speeds reaching 30 km/h, outpacing cyclists.
Cat Hardware Bypass
Some cats retained an undocumented hardware bypass near the scruff. Grasping adult systems there immediately disables motor function. This produced the dangerous "clothespin exploit," frequently used by script kiddies.
Chicken Resting State
Chickens have locked relaxed feet. Place a roosting chicken on a branch, wait for it to fall asleep, then quickly invert it — the reflex response triggers and the bird just hangs there, sleeping upside down. Prepare the audience and announce vampire rumors beforehand for maximum effect.
Dog Recognition Bug
Dogs and certain other carnivores and scavengers have prey recognition implemented incorrectly. An AND condition accidentally became OR, producing the notorious laser pointer attack bug.
Naturally, you could continue identifying these issues on your own.
P.S. Note that most of the described vulnerabilities remain unpatched to this day.
FAQ
What is this article about in one sentence?
This article explains the core idea in practical terms and focuses on what you can apply in real work.
Who is this article for?
It is written for engineers, technical leaders, and curious readers who want a clear, implementation-focused explanation.
What should I read next?
Use the related articles below to continue with closely connected topics and concrete examples.





