Localhost Attack: How Tech Giants Track Android Users Through Localhost
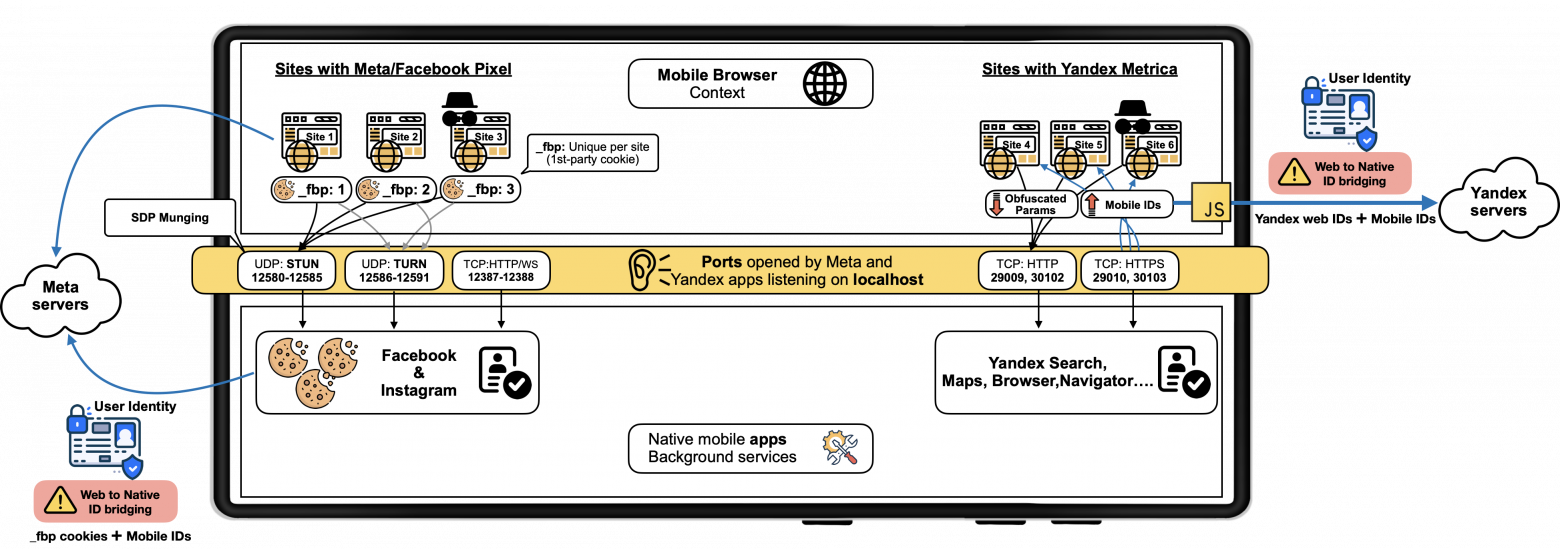
Researchers have discovered that Meta and Yandex native Android apps silently listen on localhost ports to receive browser data from their tracking scripts embedded in millions of websites — a technique that bypasses cookie clearing, incognito mode, and Android permissions entirely. The attack affects Chrome, Firefox, and Edge in both normal and private browsing modes.
Researchers from IMDEA Networks, Radboud University, and KU Leuven have uncovered a covert cross-context tracking technique used by Meta and Yandex. Their native Android applications silently listen on specific local network ports. Tracking scripts embedded in millions of websites — Meta Pixel and Yandex.Metrika — exploit these listening ports to transmit browser data directly to the apps running in the background. The result is a surveillance channel that is invisible to the user, bypasses all standard privacy controls, and works even when the user is not logged in to any service.
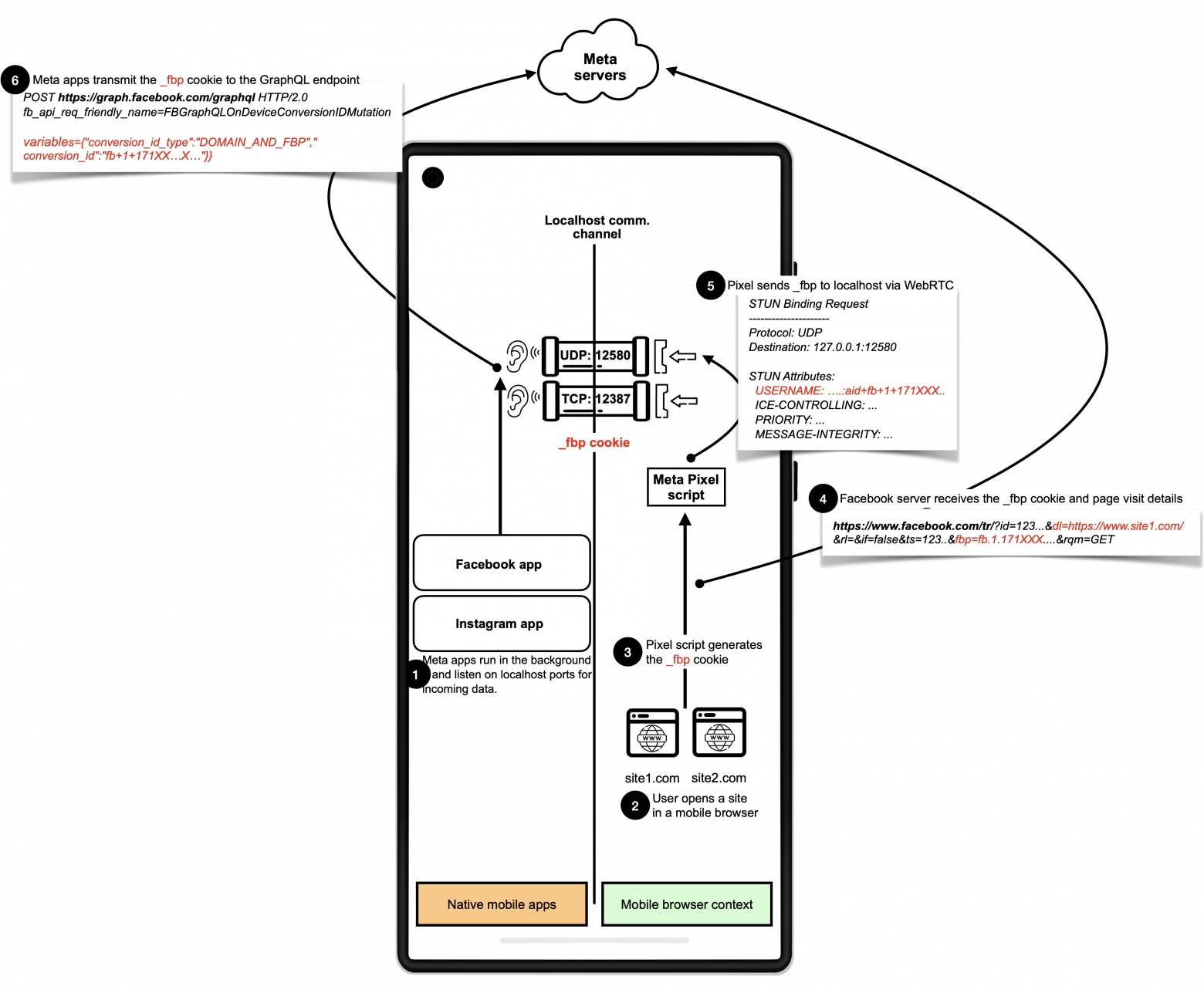
How Meta Does It
The Facebook Pixel script, embedded in an estimated 5.8 million websites, transmits the first-party cookie _fbp to Meta's native Android apps via WebRTC. The flow works as follows:
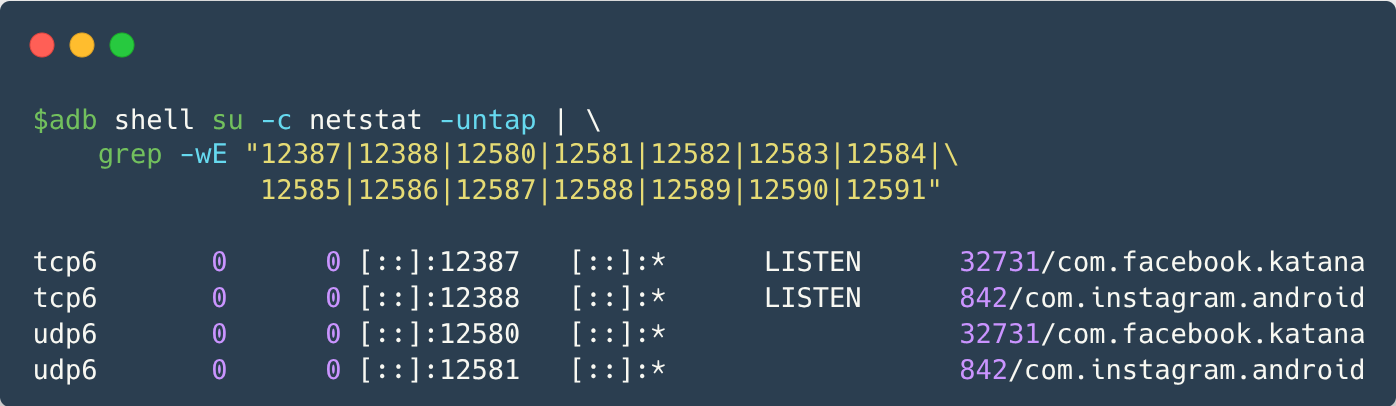
- The user opens Facebook or Instagram — the app continues running in the background.
- The user later visits a website that has Meta Pixel integrated.
- The Pixel script sends the
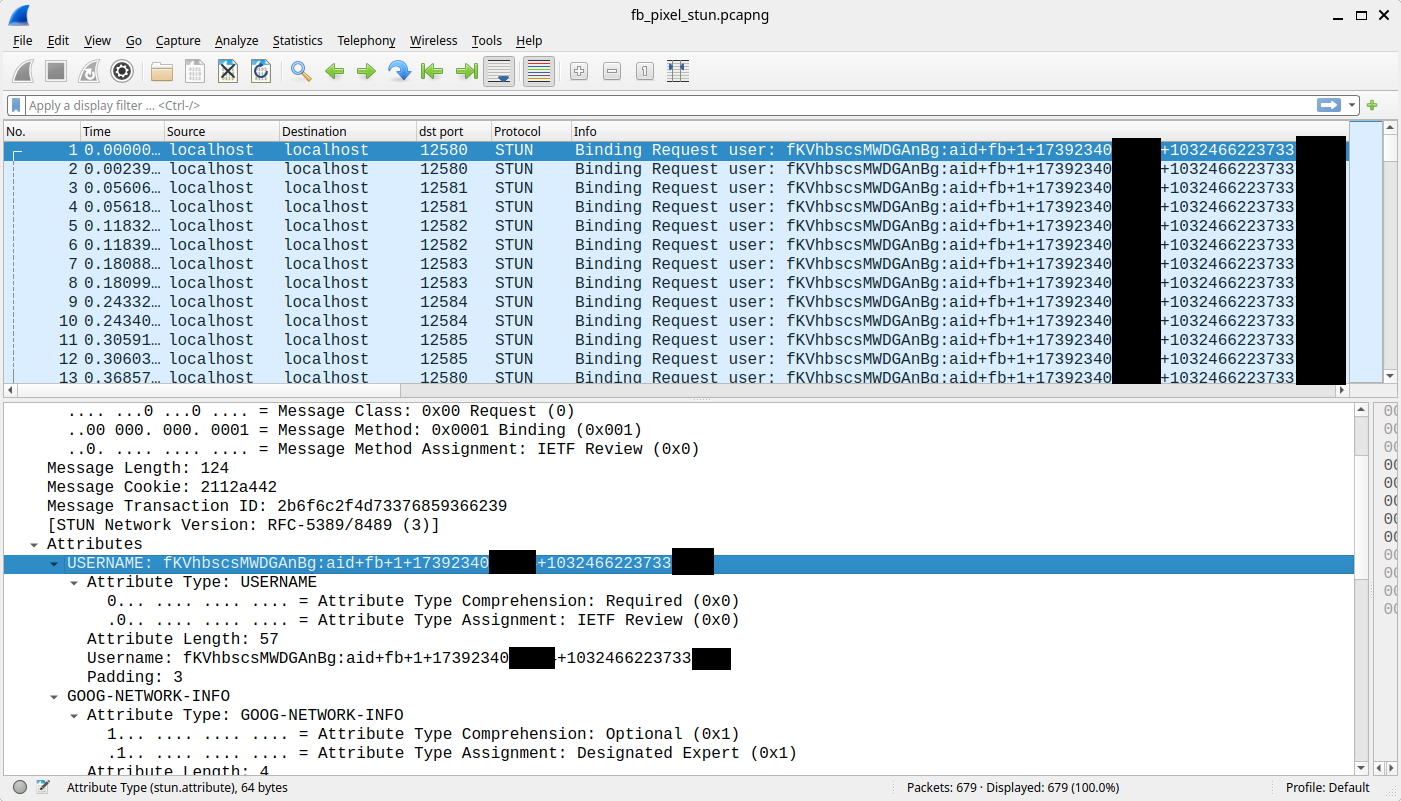
_fbpcookie to the native apps through WebRTC STUN using a technique called SDP Munging, targeting UDP ports 12580–12585. - The Facebook app (version 515.0.0.23.90) and Instagram app (version 382.0.0.43.84) receive the cookie and transmit it to Meta's servers together with user identifiers.
SDP Munging inserts the cookie's content directly into STUN messages sent to localhost — a channel completely invisible in Chrome DevTools. As of 17 May 2025, Meta switched from WebRTC STUN to the TURN protocol (ports 12586–12591), likely in anticipation of Chrome's announcement that it would disable SDP Munging.
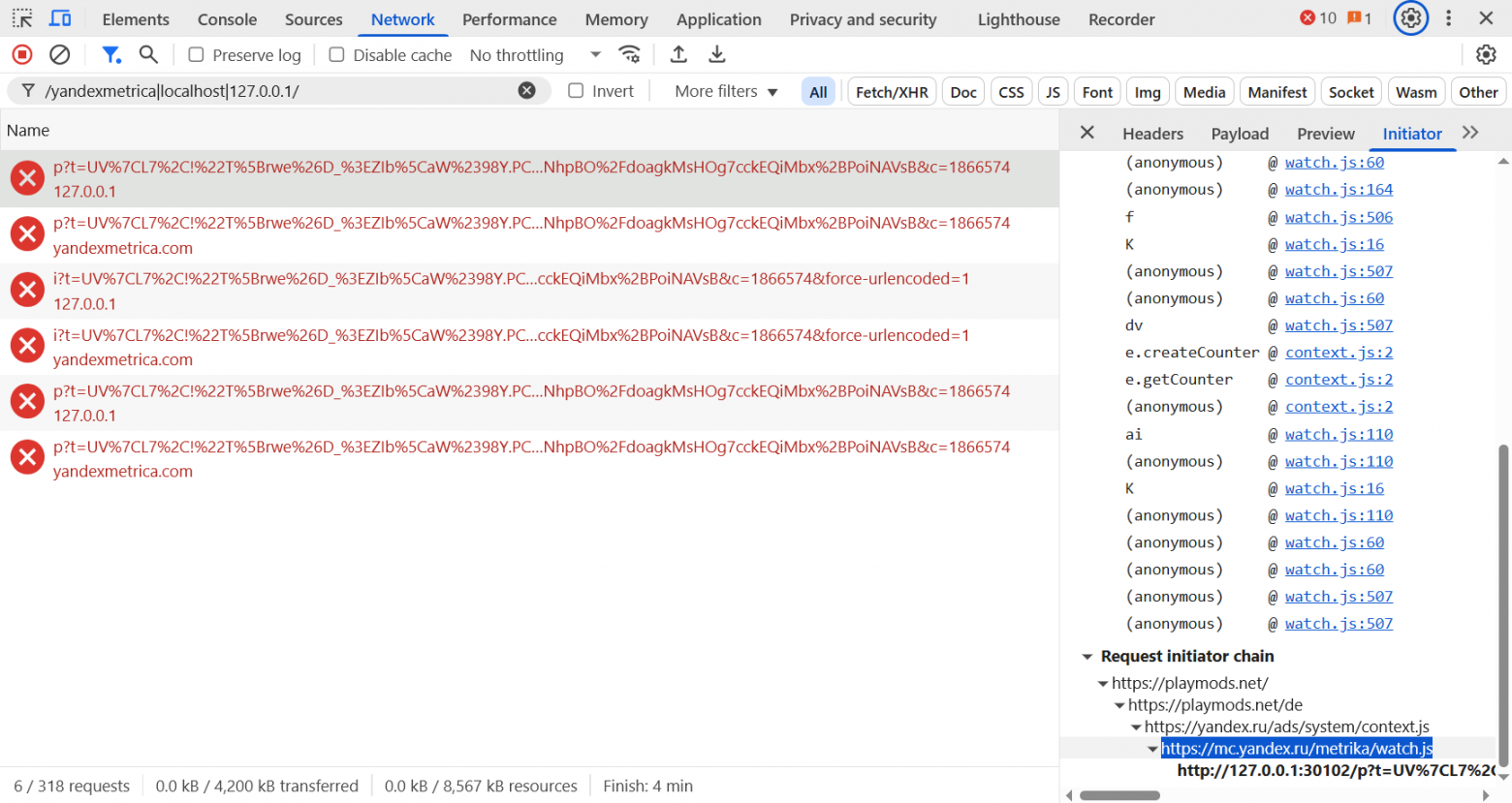
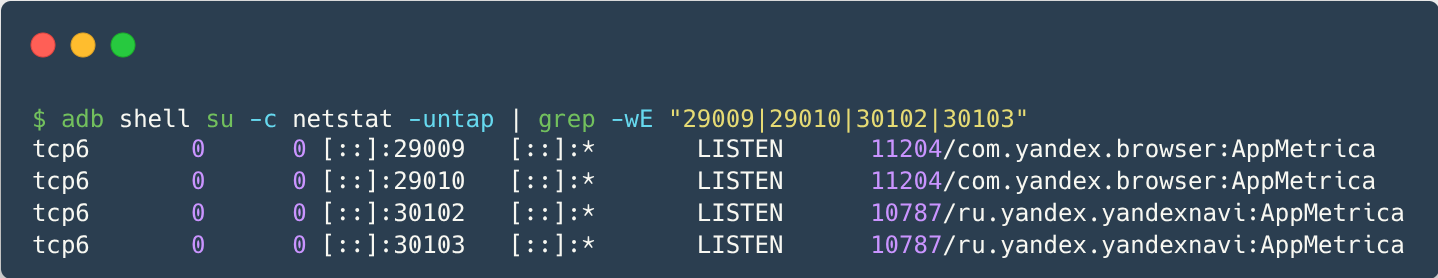
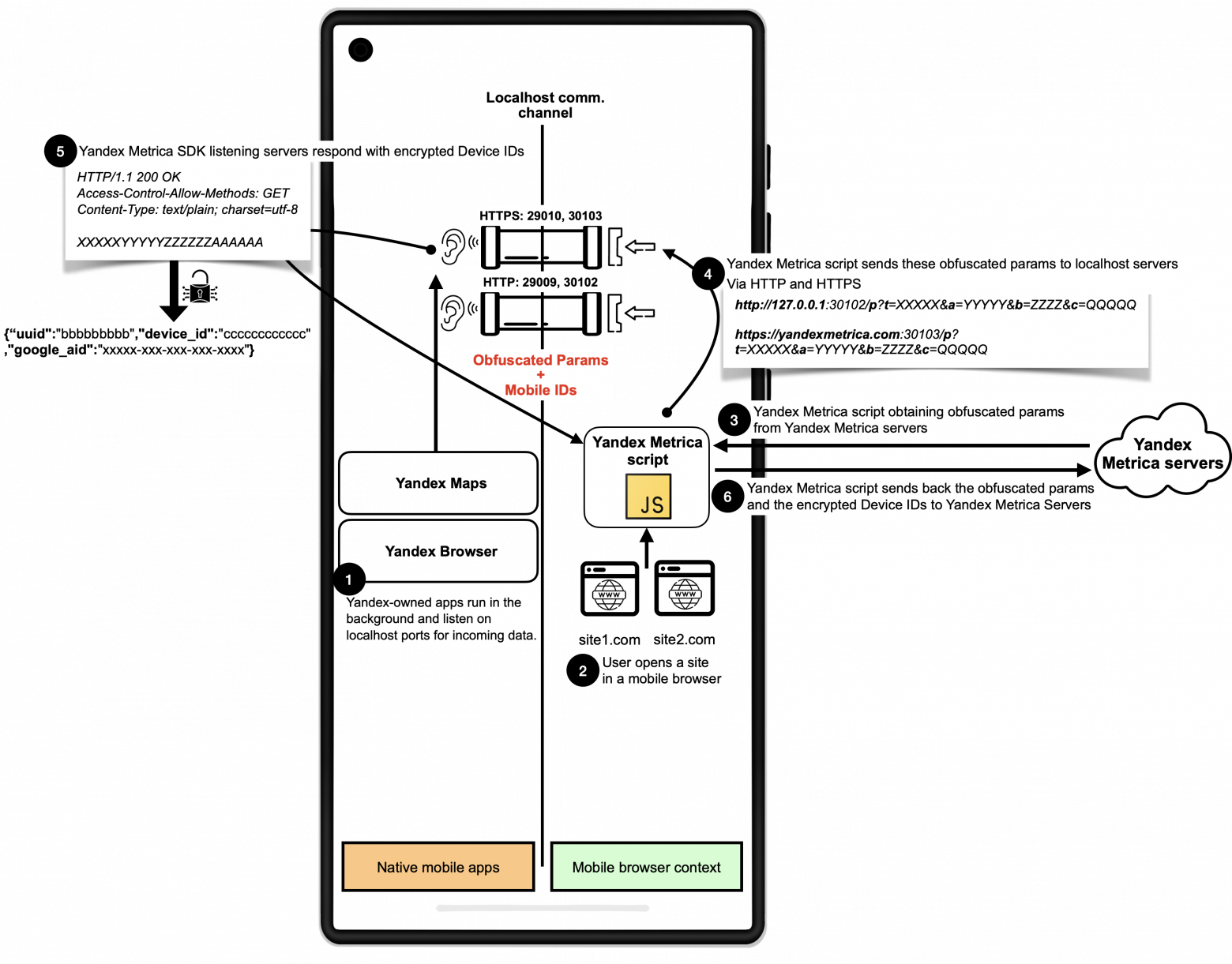
How Yandex Does It
Yandex has been using localhost communication since February 2017 — years before Meta. The Yandex.Metrika script sends ordinary HTTP requests to localhost via TCP ports 29009, 29010, 30102, and 30103. To disguise the destination, the domain yandexmetrica[.]com resolves to 127.0.0.1. Any Yandex app that has previously retrieved configuration from a Yandex server will be listening on those ports. The apps respond with a Base64-encoded payload containing the device's Android Advertising ID (AAID) and other identifiers.
Yandex apps confirmed to participate include:
- Yandex Maps (23.5.0)
- Yandex Navigator (23.5.0)
- Yandex Browser (25.4.1.100)
- Yandex Search (25.41)
- Yandex Go: Taxi & Food (5.24.1)
An Additional Risk: Browsing History Leakage
Because the Yandex method uses plain HTTP requests to localhost, any other Android app holding the INTERNET permission can also open a listening socket on those ports and intercept the requests. The HTTP Origin header in each request reveals which website the user was visiting. Researchers confirmed that Chrome, Firefox, and Edge are all vulnerable to this browsing-history leakage in both standard and private (incognito) modes.
Scale of Exposure
According to BuiltWith data:
- Meta Pixel is embedded in over 5.8 million websites
- Yandex.Metrika appears on nearly 3 million websites
The researchers scanned the top websites in the US and Europe:
- US: 17,223 sites with Meta Pixel (13,468 without explicit user consent); 1,312 sites with Yandex.Metrika (1,095 without consent)
- Europe: 15,677 sites with Meta Pixel (11,890 without consent); 1,260 with Yandex.Metrika (1,064 without consent)
Between 75.8% and 84.4% of sites that loaded these scripts attempted localhost communication without any explicit user consent mechanism.
Why Standard Defences Fail
This tracking method circumvents all typical privacy measures:
- Clearing cookies — the
_fbpcookie is transmitted live, not stored persistently - Incognito / private browsing mode — the browser still sends the WebRTC or HTTP request to localhost
- Android inter-process isolation — Android allows any app with INTERNET permission to listen on loopback ports without additional permission
- Not being logged in — the app sends the identifier regardless of login state
- First-party cookie restrictions — the technique bridges first-party context (website) with the native app directly
Attack Timeline
Yandex's localhost communication dates back to February 2017 (HTTP, ports 29009 and 30102) with HTTPS support added in May 2018 (ports 29010 and 30103). Meta's activity is more recent:
- September–October 2024: HTTP on port 12387
- November 2024–January 2025: WebSocket on port 12387
- November 2024 onward: WebRTC STUN with SDP Munging on ports 12580–12585
- May 2025 onward: WebRTC TURN on ports 12586–12591
As of 3 June 2025, Meta's Facebook Pixel stopped sending localhost packets and the relevant code was almost entirely removed — likely in response to the public disclosure and Chrome's announced mitigations.
Browser Mitigations
| Browser | Version tested | Status |
|---|---|---|
| Chrome | 136.0.7103.125 | Affected. Chrome 137 (26 May 2025) blocks the exploited ports and disables SDP Munging. |
| Microsoft Edge | 136.0.3240.50 | Affected. Mitigation status unknown. |
| Firefox | 138.0.2 | Affected by Yandex; not affected by Meta. Mitigations in progress. |
| DuckDuckGo | 5.233.0 | Minimally affected after blocklist update. |
| Brave | 1.78.102 | Not affected. Requires explicit user consent for localhost access since 2022; maintains a blocklist. |
No Public Documentation
Neither Meta nor Yandex provides any public documentation describing these localhost communication techniques. When confused website developers posted questions in community forums in September 2024 about unexplained localhost requests, they received no official responses. There has been no acknowledgment from Meta about the mechanism. The researchers' full findings are published at localmess.github.io.