How I Discovered a Hidden Microphone in a Chinese NanoKVM
A security researcher tears down the affordable NanoKVM hardware KVM switch and discovers an undocumented microphone, hardcoded encryption keys, pre-installed hacking tools, and communication with Chinese servers — raising serious questions about supply chain trust.
The NanoKVM is a hardware KVM switch created by the Chinese company Sipeed. This compact device allows remote management of computers and servers via a virtual keyboard, mouse, and monitor. Thanks to its low cost (approximately 30-60 euros) and the promise of open-source code, the device attracted significant attention from the internet community.
How the Device Works
The device is equipped with an HDMI connector, three USB-C ports, an Ethernet jack, and a special serial interface. After connecting to the internet, access is provided through a web browser. The NanoKVM allows you to:
- View the target computer's video output through a browser
- Emulate keyboard, mouse, CD-ROM, and USB drives
- Enter BIOS and manage the computer's power
- Install operating systems remotely
The key difference from RDP or VNC: no software installation is required on the target machine.

Security Problems
The author identified numerous serious vulnerabilities:
Critical flaws:
- The device initially shipped with default passwords, and SSH access was enabled automatically
- The encryption key for protecting passwords is hardcoded and identical across all devices
- No protection against CSRF attacks
- Session invalidation is impossible
- The device uses Chinese DNS servers, with difficult custom configuration
- It exchanges data with Sipeed servers in China
- It does not verify the integrity of software updates
- It contains network packet analysis tools (tcpdump, aircrack) in the production build
The Hidden Microphone
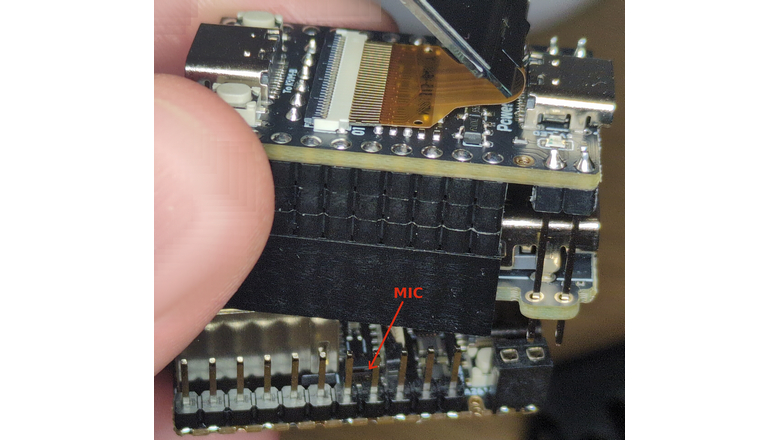
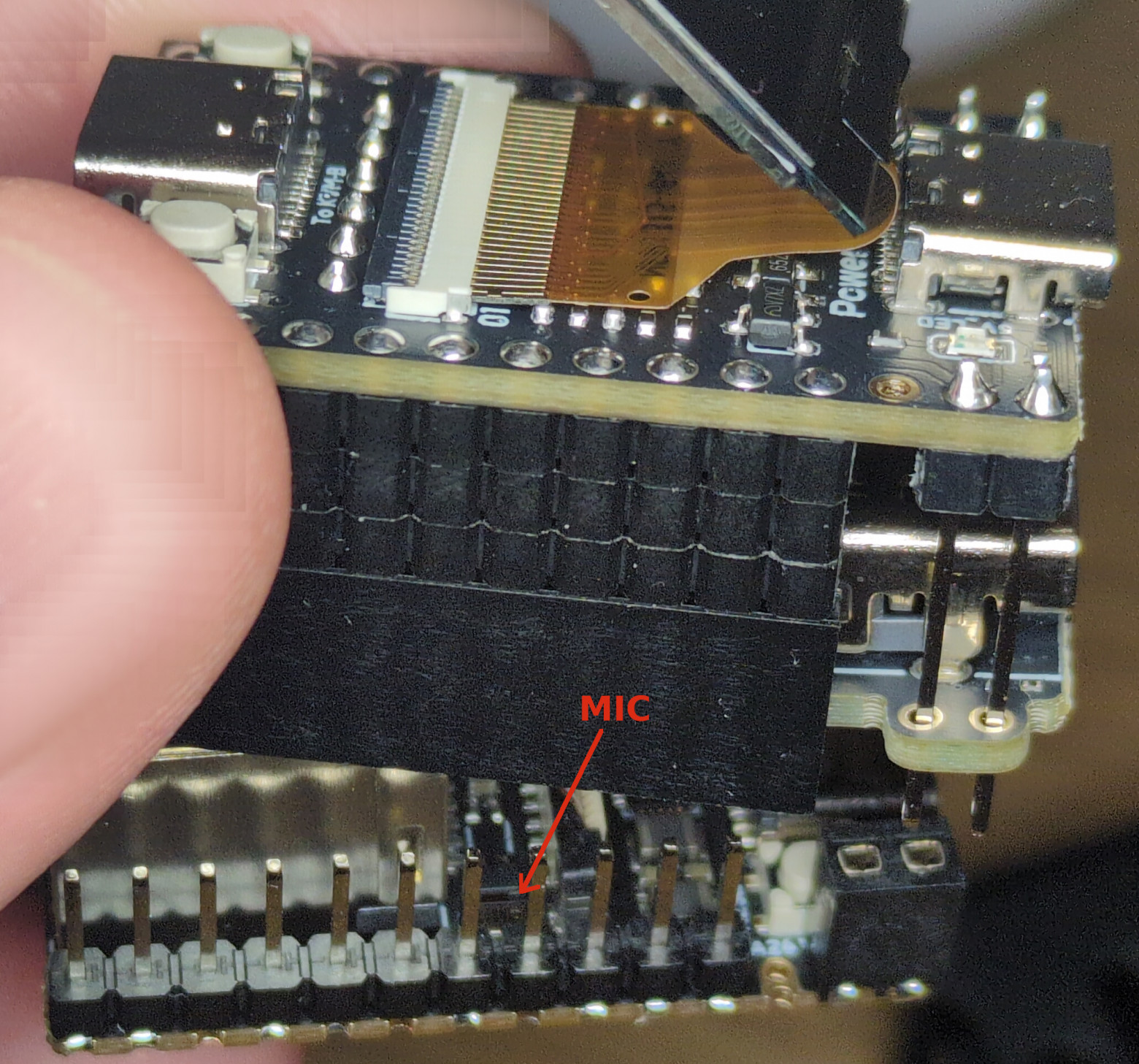
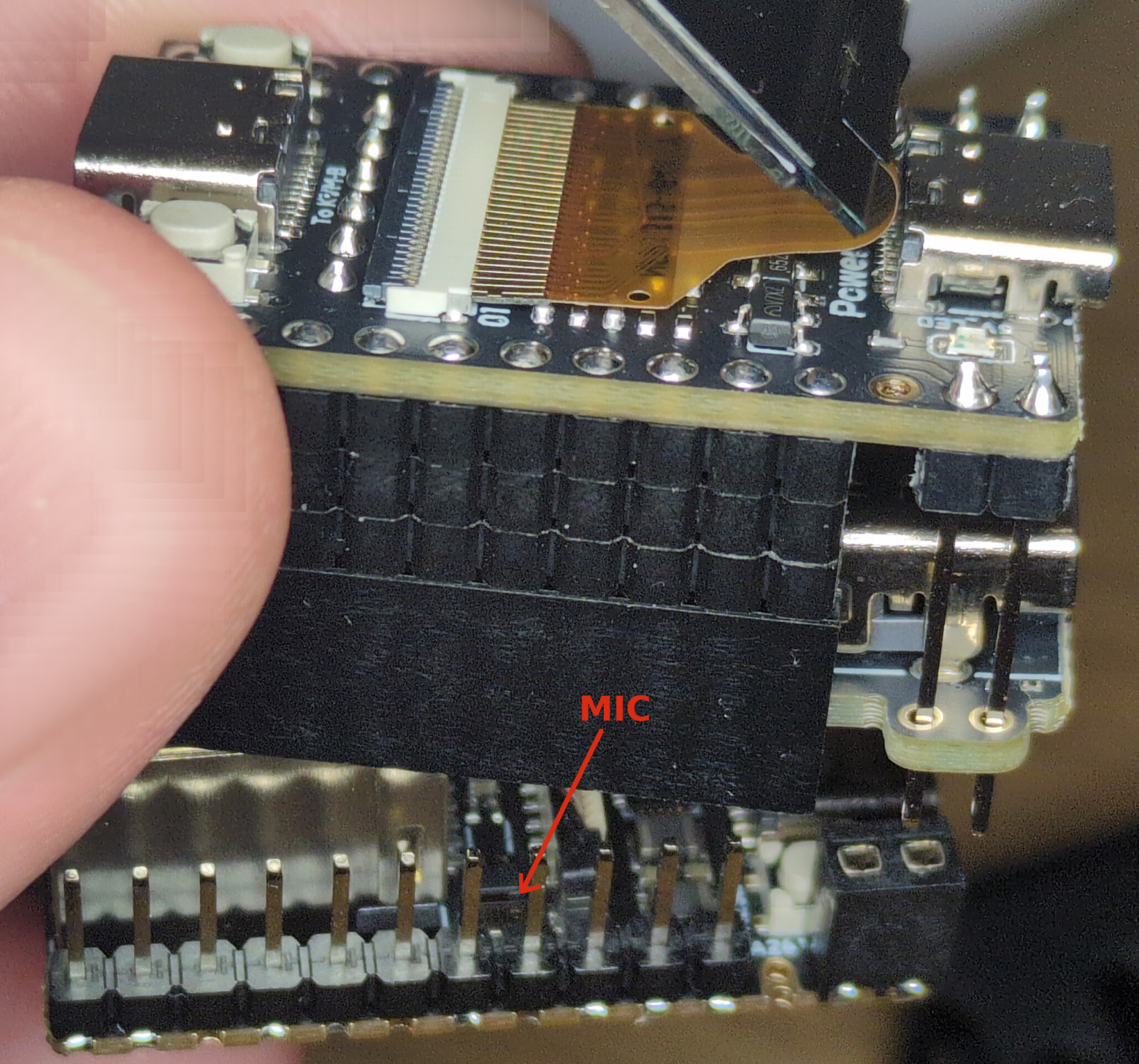
The most alarming discovery was a built-in microphone measuring just 2x1 mm, not mentioned in the official documentation. The component is capable of recording high-quality audio.
The critical issue: all the necessary tools for recording were pre-installed. Via SSH, one could use the following commands:
amixer -Dhw:0 cset name='ADC Capture Volume' 20
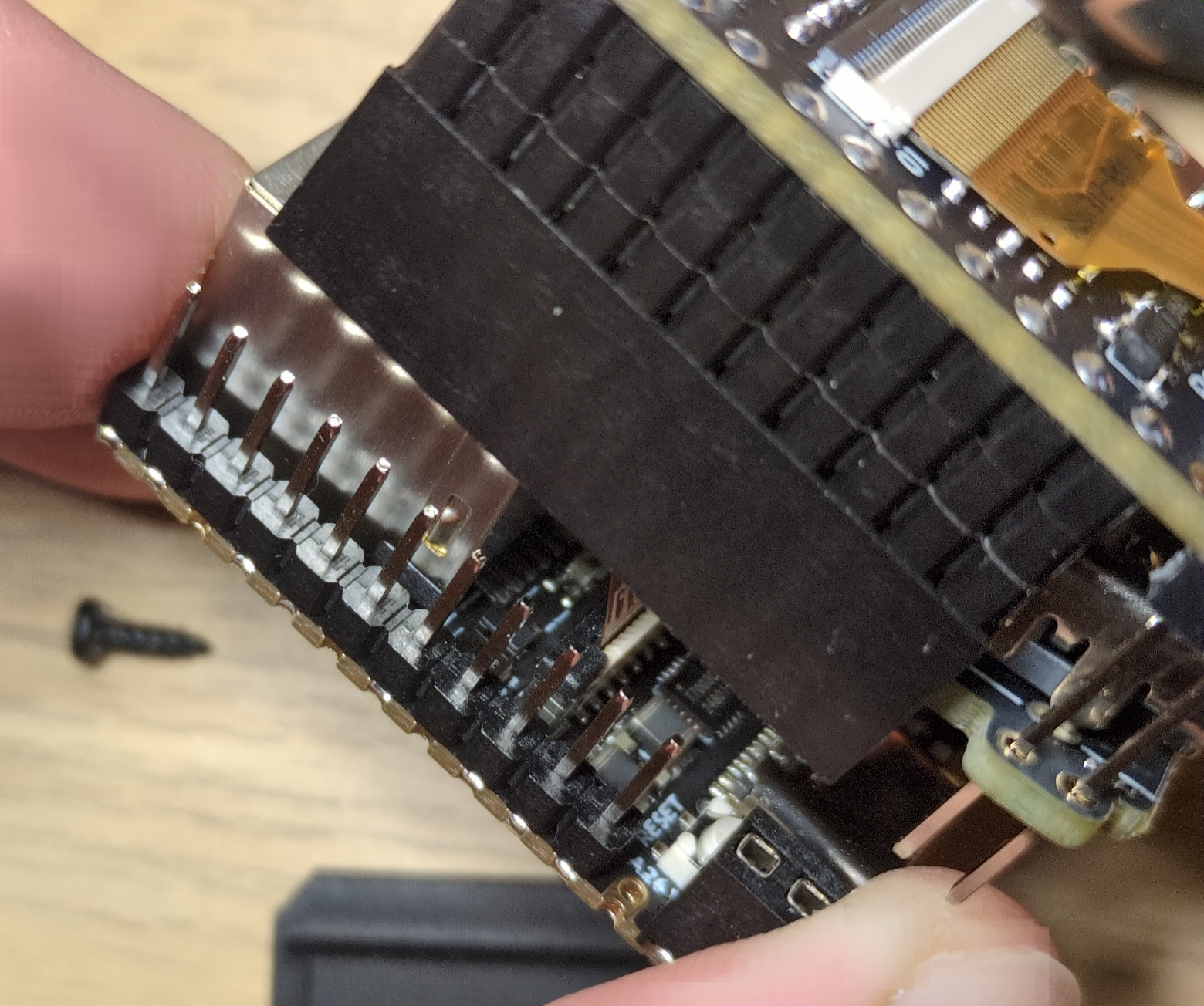
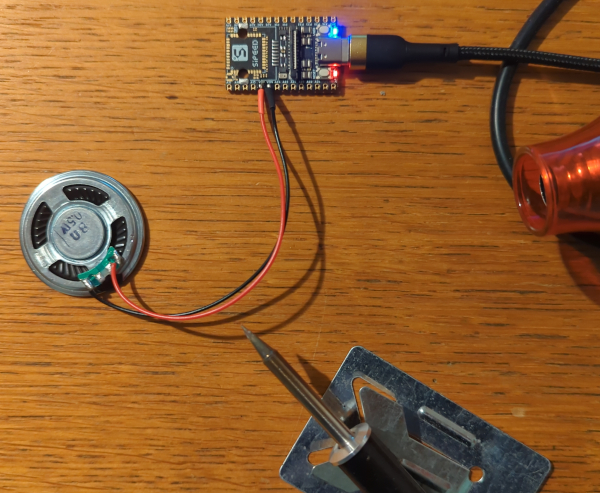
arecord -Dhw:0,0 -d 3 -r 48000 -f S16_LE -t wav test.wav & > /dev/null &This allows recording audio or streaming it over the network in real time. Physically removing the microphone is difficult — it requires a microscope and micro-soldering skills.
Analysis
The author believes the problems are caused by carelessness and development haste rather than malicious intent. However, the combination of factors — default passwords, communication with Chinese servers, hacking tools, and a hidden microphone — raises serious concern.
Possible Solutions
Since the device runs on open-source RISC-V architecture, alternative solutions exist:
- Porting your own Linux distribution (e.g., Debian/Ubuntu)
- Physically extracting the built-in SD card and reprogramming it
- Removing the microphone during disassembly
- Connecting a speaker instead of the microphone
The Bigger Picture
The author raises a broader question: how many other devices might contain hidden functionality? He cites examples of problems with Apple (Siri recording private conversations) and Google, reminding us that security concerns are not limited to Chinese manufacturers alone. American companies also have obligations to cooperate with the state, as confirmed by examples from the Global Police Summit, where Apple trained police to use iPhones for surveillance.