How I Cracked a Smart Lock Five Ways in Five Minutes
A hands-on security teardown of a ~2,000-ruble "smart" door lock reveals five distinct attack vectors — from marketplace photo reconnaissance to a 15-second physical bypass using two needles. Fancy biometrics and Bluetooth can't save a device whose entire control board is glued to the outside with double-sided tape.
Imagine installing a fancy "smart" lock on your door. Biometrics, access cards, PIN codes — a whole arsenal of protection in a compact body. Sitting behind such a door, you start to feel like the hero of a spy movie: access strictly by fingerprint, no accidental guests — almost a secret bunker. And then it turns out that all this cyberpunk protection can be bypassed in five different ways in a matter of minutes. Not by Hollywood hackers, but by an ordinary neighbor with a screwdriver. The feeling of security evaporates instantly, and the "fortress of the future" begins to look like cheap cardboard scenery.
Today we'll crack open one such "smart" lock and analyze five attack vectors that demonstrate how a beautiful technological shell doesn't always mean real protection. Get ready — this will be both educational and, at times, absurd.
Anatomy of the Patient: What's Inside?
Before breaking in, you need to understand how the victim is built. Knowledge of anatomy is half the success of any surgeon. And any hacker too.
Level One: Good Old Mechanics
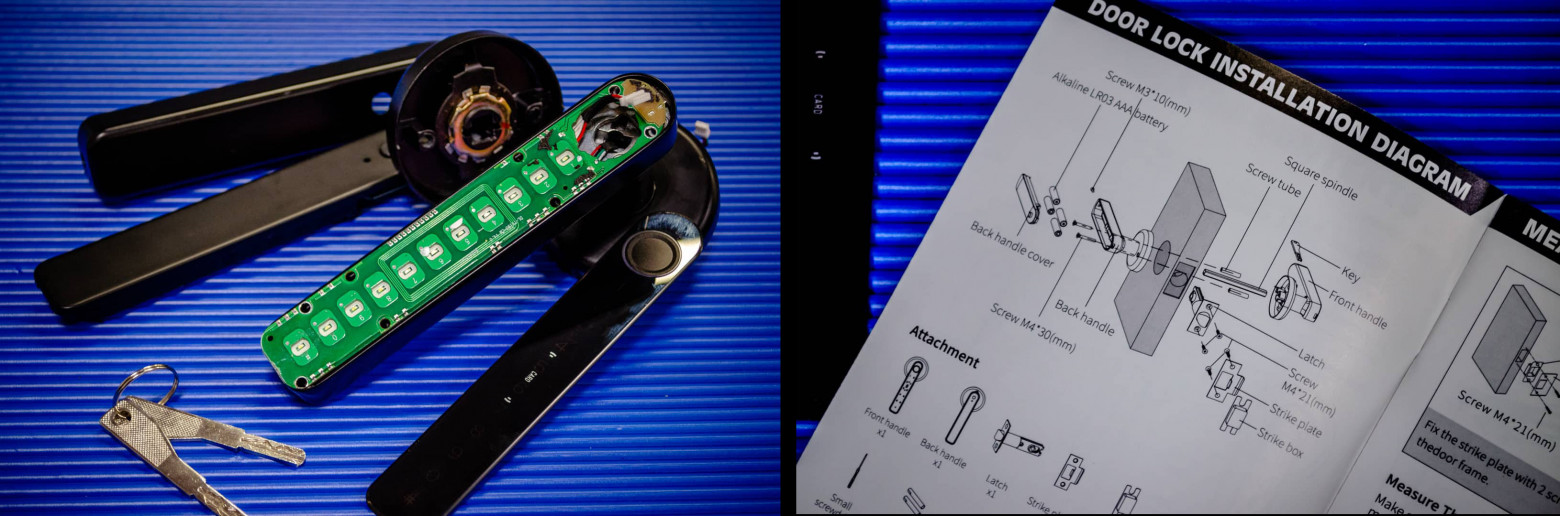
Let's start with mechanics — the basic construction level. The lock consists of three main parts: the inner handle, the cylinder, and the outer handle. They are connected by a square rod-shaft.
When the lock receives a command to open (via code, card, fingerprint, or Bluetooth), an electric motor extends a miniature metal latch. This latch works like a clutch in a car — it physically connects the outer handle to the shaft. Now turning the handle is transmitted to the shaft, and the door opens. After that, the latch retracts, and the handle goes back to standby mode waiting for the next open command.
In case of complete electronics failure, a classic mechanical key is provided. It is inserted into a separate cylinder on the end of the handle and actuates the latch in a good old-fashioned mechanical way.
You might already guess what's wrong here. But that's not all.
Level Two: The Electronic "Brain"
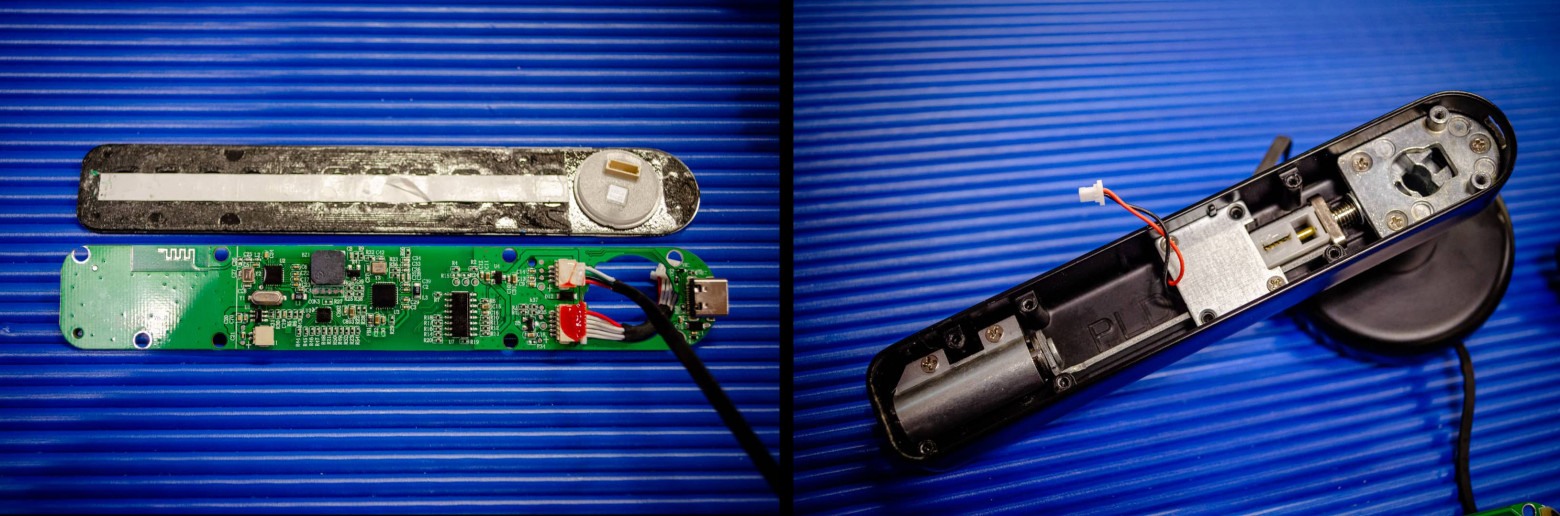
Now for the electronics. All of it is compactly packaged and sits right inside the handle.
In the inner part of the handle — the one on the protected room side — there is a compartment for four AAA batteries and a couple of buttons.
The large button puts the lock into "always open" mode: hold it for three seconds and the mechanism unlocks. The second, hidden in a hole, is the factory reset button. Press it with a needle, hold for five seconds, and the lock returns to its original state.
The outer, street-facing part of the handle is where all the interesting stuff is. This is where all the "brains" of the lock live: the main board and controllers. Imagine placing the control unit of a home alarm system not inside the house, but in the mailbox at the gate. Convenient for checking, but not very secure.
What do we see inside this "mailbox"? The main board — the brain that makes all decisions. Input devices — a touch keypad for PIN code, fingerprint scanner, and card reader for access cards. A wireless module — Bluetooth for smartphone connectivity. A USB-C port for emergency power (not for data). Under the board hides the actuator — that very small motor with the latch.
From the board to the inner handle, through a hole in the shaft, runs a harness of four wires (red, black, green, white). They handle power and signals from the buttons on the inner handle.

Cascade of Vulnerabilities: From Digital Copies to Physical Access
Now that we know the patient's anatomy, we can start the pentest. And believe me — there's a whole bouquet of problems waiting for us.
Vector 1: "Thanks for the Review!"
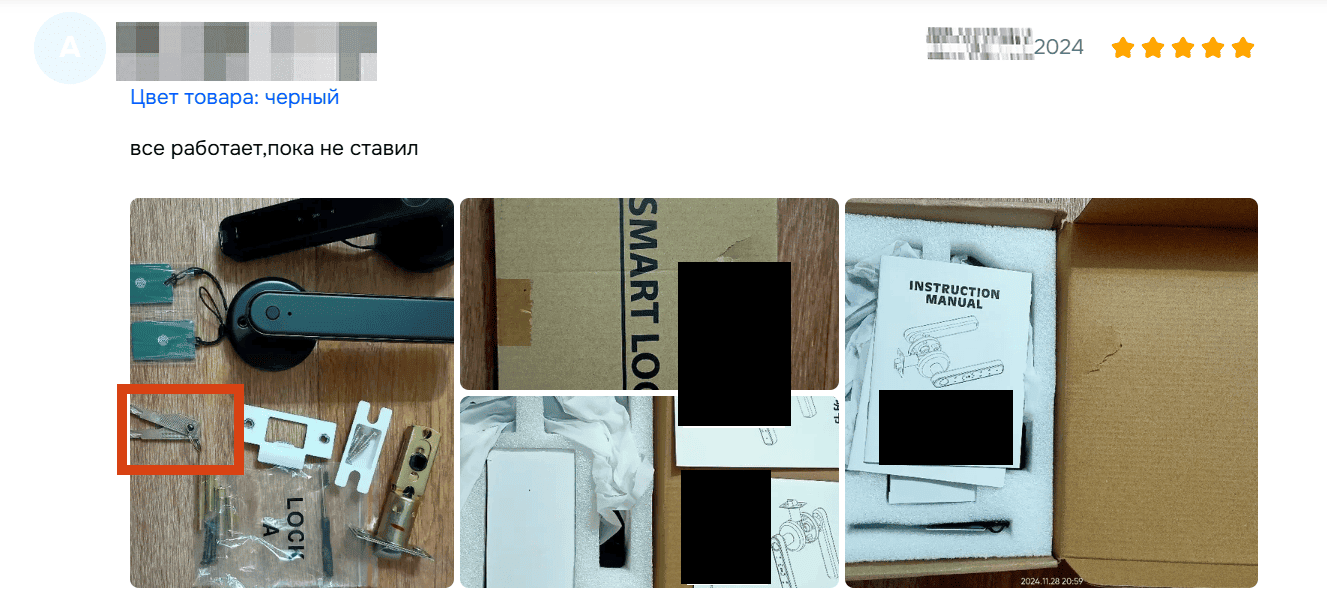
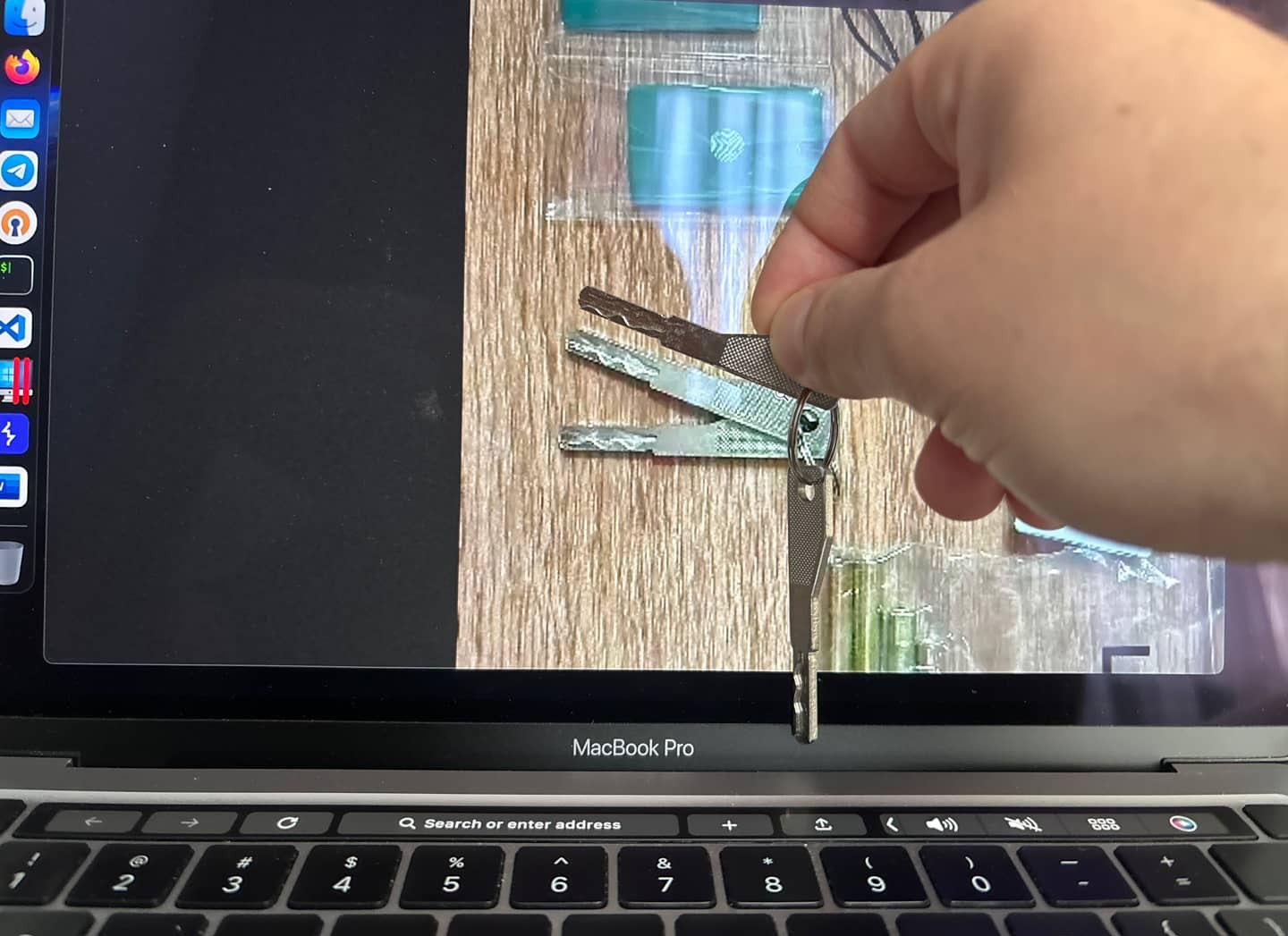
Let's start with the simplest — the human factor. Some lock buyers leave reviews on marketplaces — sometimes even with photos. And in a burst of enthusiasm they may photograph not just the handle, but also the keys. This is our first entry point.
Here's a typical example: a review on a popular platform, and in the frame — a key.

We enlarge the image, trace the key profile right from the screen, and head to the nearest locksmith. A duplicate of such a key will be made for a couple hundred rubles. Elementary.
And you don't even have to go to that trouble. Mechanical keys are generally not unique. Factories mass-produce locks with a limited number of combinations. Keys like ours typically have about 200–500 variations. Security is partly ensured by the fact that locks with identical keys try not to be shipped in the same batch to the same city. But judging by the fact that we found a duplicate of our key among marketplace photos, the manufacturer may have skimped on the number of combinations.
Vector 2: DIY CSI
Now let's look at the keypad. Black glossy plastic that only looks good in the manufacturer's catalog. In reality, the panel is always covered in greasy fingerprints. And those traces are our second vector.
The algorithm is simple: come to the lock with a cloth, carefully wipe the panel, wait for the owner to enter the code, come back and analyze the fresh fingerprints. By shining the panel at a certain angle with an ordinary smartphone flashlight, you can clearly see which digits were touched.

Of course, there remains the problem of digit sequence. On the lock under study, the PIN code can consist of 6–10 digits, but the fingerprints sharply reduce the search space.
For example, if an attacker knows for certain that the code is six digits long and sees traces on six different keys, they need to try 6! = 720 combinations. Such a set can be checked manually in a reasonable time.
However, the scenario with a six-digit code without repetition is the simplest for an attacker. In reality, digits in the combination may repeat — and then the number of combinations grows significantly: 6^6 = 46,656.
So the method can hardly be called a "cheat code" for instant cracking — but it shouldn't be dismissed either. It's not a silver bullet, but rather a useful addition to the attacker's arsenal.
Vector 3: James Bond Style
Nobody reads manuals, right? But I do — and that's how I know the lock's firmware has its own little "easter egg."
The combination 888# puts the lock into initialization mode. If after entering it a legitimate user opens the door within 10 seconds using their usual method (finger, card), the lock goes into an "always open" state until the next command.
Under certain circumstances, this can be exploited. I, as an attacker, approach the door 5 seconds before you and enter 888#, pretending I'm just pulling on the handle. You approach, say the door is locked, put your finger on it, open the door and go inside. Congratulations — you just left the door unlocked for me or my accomplice.
Vector 4: The Golden Key
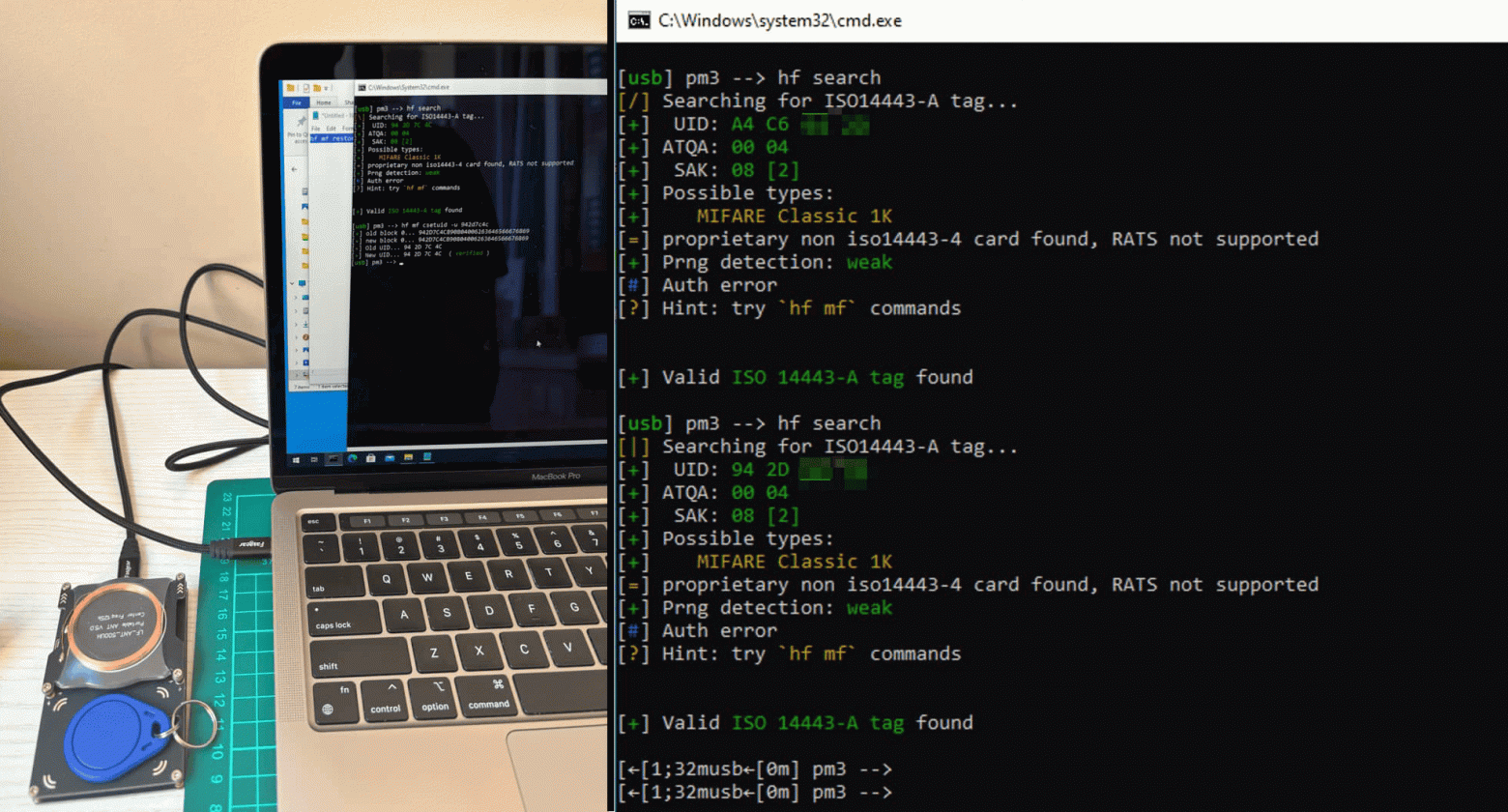
The fourth method — working with access cards. Our test subject uses Mifare Classic 1K format cards. This is an old and long-compromised standard. Using a device like a Flipper Zero or Proxmark, you can read a card in a couple of seconds and create an exact copy on a blank. The lock won't notice the substitution. Not great.
Vector 5: Physical Bypass — The Cherry on Top
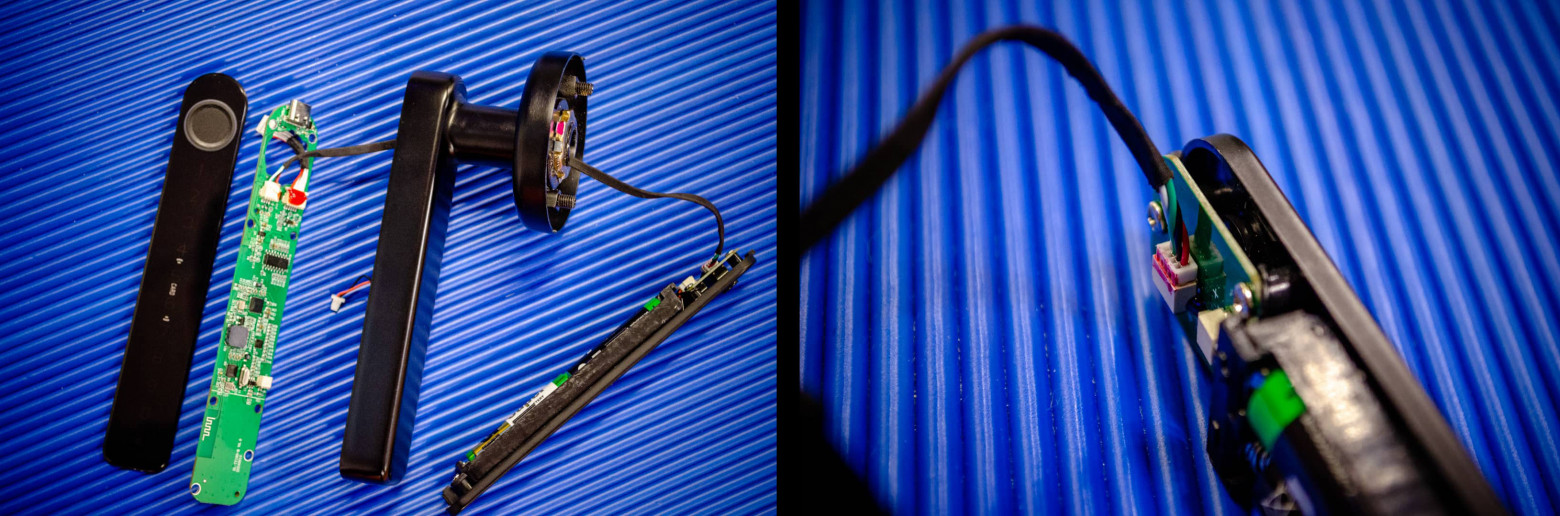
And here is the attack that makes all the previous methods simply redundant. Let's go back to the mechanism. All the "brains" of the lock — controller, wires, electronics — are located outside, in the public zone. And protecting all this wealth is... a plastic cover held on by double-sided tape.
This isn't even security theater — it's amateur hour.
Take any thin and sturdy object: a box cutter, a plastic card, or a professional case opening tool. A couple of moves — and the cover is off. Under it is the board with all the contacts.
We remember the four wires going inside. One of them (in our case white) is responsible for the signal from the inner open button, and another (black) is ground. Take two needles, short the corresponding contacts directly on the board, wait three seconds — and the lock simulates pressing the button from inside. Click — and the door is open. Time to open: 10–15 seconds.
This opens the door to creativity. As an attacker, I can quietly prepare a foothold for future attacks. What can be done?
- Solder a miniature reed switch to the open contacts. Then all it takes is bringing a magnet near a specific spot on the handle and it will open.
- A backdoor via USB — rewire the USB-C port so that connecting a cable shorts the open contacts. Walk up, plug in a cable — lock opens.
However, you don't even need to understand electronics to open the door. If you disassemble the handle all the way down (unscrew a couple more screws), you can simply push the mechanism that turns the pin with a screwdriver.
Recommendations: How This Should Work
After everything we've seen, it's obvious — the lock is architecturally designed incorrectly. Ideally, such a system should be built completely differently.
- All electronics inside the protected space. The controller, wiring, and control mechanisms must be physically inaccessible from outside.
- Only interfaces outside. Card reader, scanner, buttons. No critical logic.
- Proper mounting. Countersunk screws, protected rivets — anything except tape.
- Randomized service codes. Remove the
888#backdoor or make the code unique per device. - Tamper protection. Add case-opening sensors that send notifications to the administrator.
However, the longer you look at this construction, the clearer it becomes: this particular product cannot be fixed. It was built, as engineers say, badly by design.
Conclusion: Security Theater in Its Purest Form
What do we end up with? A device that creates the illusion of protection while providing no real security. The manufacturer stuffed the gadget with trendy technologies (Contactless cards! Biometrics! Bluetooth!) but forgot the basics of sound engineering.
This smart handle costs about 2,000 rubles. Maybe I'm asking too much for that price? But compare it against a regular mechanical lock at the same price point in terms of attack vectors. And the question immediately arises — should every device be made "smart"?
Answering the main question: can you use it? If you're okay with any motivated person with a knife and a couple of needles walking into your home in under a minute — then yes. Otherwise, stay away.
This article was written exclusively for educational purposes. Tampering with someone else's locks is illegal. Use the knowledge gained to choose more reliable solutions, not for unlawful actions.



